Contextual and Timely Threat Intelligence
Strategic Threat Intelligence Transformation Roadmap
In the realm of cybersecurity strategy, threat intelligence without context is merely noise, and intelligence without proper timing is often irrelevant. The true power of cyber threat intelligence lies not in the volume of indicators collected, but in the precision with which we apply contextual understanding and temporal awareness to transform raw data into strategic advantage.
Context: The Strategic Filter
Context serves as the critical lens through which threat intelligence becomes actionable business intelligence. A sophisticated APT campaign targeting critical infrastructure may represent an existential threat to an energy company while posing minimal direct risk to a retail organization—yet both may receive identical threat feeds. Strategic utilization of threat intelligence demands that we move beyond generic advisories to develop contextually-aware intelligence that considers our specific threat landscape, business model, digital assets, and adversarial motivations.
This contextual awareness extends beyond technical vulnerabilities to encompass business context: regulatory environment, competitive positioning, geopolitical factors, and organizational risk tolerance. When threat intelligence is properly contextualized, it transforms from a reactive security measure into a proactive business enabler, informing everything from investment priorities to market expansion strategies.
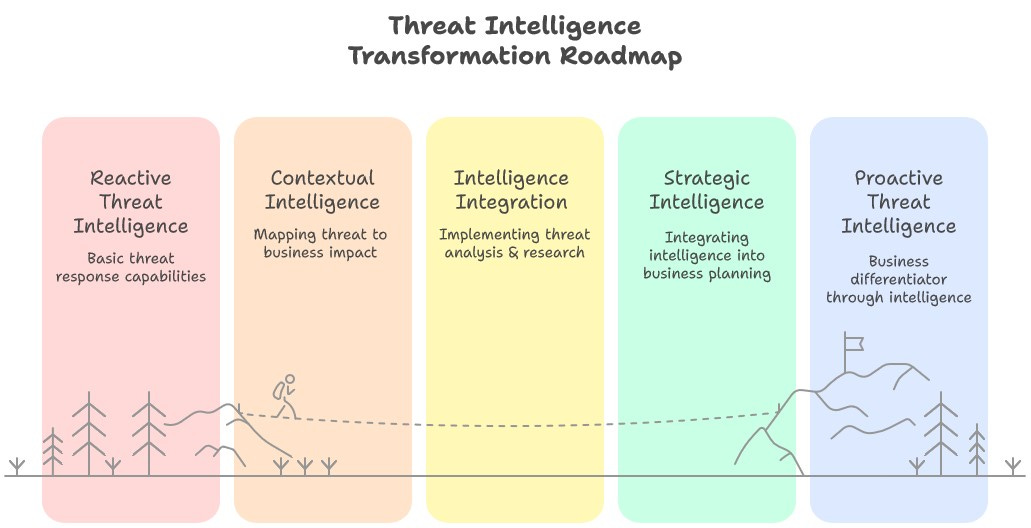
Threat Intelligence Transformation Roadmap
But how to transform and mature an existing CTI program or to establish a new one?
The following phased progression should help transform cybersecurity from a reactive expense into a strategic business capability that enhances organizational resilience, competitive positioning, and stakeholder confidence.
Phase 1: Foundation Building
Establish baseline reactive capabilities by implementing automated threat feed ingestion and basic indicator matching across security tools
Centralize threat data collection from internal sources (SIEM, EDR, network monitoring) and external feeds to create a unified intelligence repository
Define organizational context parameters including critical assets, business processes, regulatory requirements, and current threat landscape exposure
Phase 2: Contextual Intelligence Development
Map threat intelligence to business impact by correlating indicators with specific assets, processes, and potential business disruption scenarios
Develop threat actor profiling aligned to your industry, geography, and organizational profile to focus intelligence efforts on relevant adversaries
Create contextual filtering mechanisms that prioritize intelligence based on relevance to your specific threat model and business operations
Phase 3: Temporal Intelligence Integration
Implement historical threat analysis to identify patterns, seasonal trends, and campaign evolution relevant to your organization
Establish predictive intelligence capabilities using threat landscape trends to anticipate emerging risks before they manifest
Deploy dynamic threat modeling that adjusts defensive postures based on temporal threat intelligence and business cycle considerations
Phase 4: Strategic Intelligence Operationalization
Integrate threat intelligence into business planning by providing executive briefings that translate technical threats into business risks and opportunities
Develop intelligence-driven investment frameworks that prioritize security spending based on strategic threat forecasting and business value
Create competitive intelligence capabilities that leverage security insights to inform market positioning and business strategy decisions
Phase 5: Strategic Advantage Realization
Establish threat intelligence as a business differentiator by demonstrating superior security posture to customers, partners, and stakeholders
Develop intelligence-sharing partnerships that provide strategic value through industry collaboration and enhanced threat visibility
Measure and communicate the business value of strategic threat intelligence through metrics that resonate with executive leadership and board governance
Time: The Strategic Accelerator
The temporal dimension of threat intelligence operates across multiple strategic horizons. Tactical timeliness—receiving and acting upon immediate threats—represents the foundational layer. However, strategic value emerges when we leverage temporal patterns to anticipate future threat evolution and align our defensive investments accordingly.
Historical context provides the narrative thread that connects seemingly disparate incidents into comprehensible threat campaigns. Meanwhile, predictive temporal analysis enables organizations to position themselves ahead of emerging threats, turning cybersecurity from a cost center into a competitive differentiator. Organizations that master this temporal dimension don't just respond to threats—they anticipate and prepare for threat evolution, often achieving market advantages through superior security posture.
The Strategic Synthesis
The intersection of context and time creates what I term "strategic intelligence velocity"—the ability to rapidly convert threat intelligence into informed business decisions. This synthesis enables executives to understand not just what threats exist, but which threats matter to their specific organization, when they're likely to manifest, and how defensive investments should be prioritized to maximize both security outcomes and business value.
In the hands of strategic leaders, contextually aware and temporally conscious threat intelligence becomes a powerful instrument of competitive advantage—transforming cybersecurity from a necessary expense into a strategic capability that enhances market position, enables confident expansion, and demonstrates measurable business value to stakeholders and customers alike.
Ready to Transform Your Threat Intelligence Strategy?
Implementing this roadmap requires more than technical expertise—it demands strategic vision, executive alignment, and an in-depth understanding of how cybersecurity creates business value. Every organization's journey from reactive to strategic threat intelligence is unique, shaped by industry dynamics, organizational culture, and competitive landscape.
If you're ready to elevate your threat intelligence from a tactical security function to a strategic business advantage, I'd welcome the opportunity to discuss your specific challenges and objectives. Whether you're just beginning this transformation or looking to accelerate progress through particular phases, having an experienced guide can significantly reduce implementation risks and time-to-value.
Please don't hesitate to reach out to explore how we can work together to develop a threat intelligence strategy that not only strengthens your security posture but enhances your competitive position in the market. Let's transform your cybersecurity investment into a measurable business differentiator.